[Launch] Painless Android Obfuscation
R8 Configuration is painful and unreliable. Let us fix it for you.
You are receiving this mail because we exchanged emails with each other and we value your opinion. We assumed you will be interested to know what are working on and what we are thinking. We will send at most one email per month.
You can unsubscribe at any time at the bottom of the email.
This month we’re announcing the beta of our new reliable Android R8 Configuration service. We are looking for two Android apps to work with us. You can apply by answering this email.
Shrinker Configuration Problems
R8 is a standard tool in the Android build chain. It is used to obfuscate and shrink your app. It makes the code leaner, smaller, faster and prevent people from copying it.
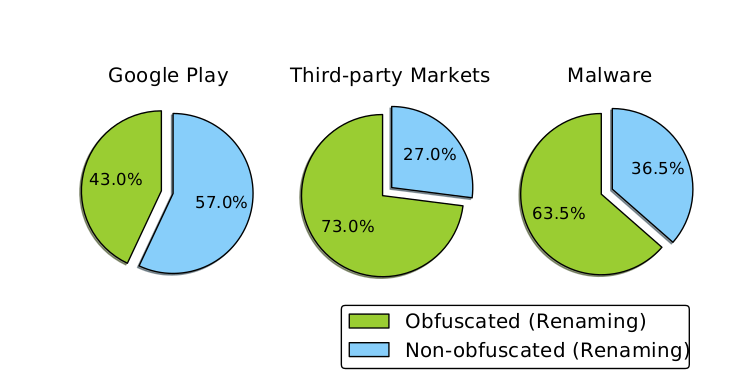
With these features and its deep integration in Android Studio, it sounds obvious to use it. Yet only 53% of app in 2018 are using an obfuscator. Why is that?
We were curious as to why so Nicolas asked 10 Android developers and they had only one answer to share:
Obfuscator configuration is horrible. It breaks all the time and our developers are spending a lot of valuable time to find and resolve bugs.
There are various obfuscators available for Android. R8 is the major one because Google installed it on all Android Studio. It replaced Proguard still widely used and loved. We support all of them but the rest of this article will assume you use R8.
Building Working R8 Configuration
We listened to you and we fixed your pain. Stop wasting your developer time by asking them to build this file.
We build for you a reliable and working obfuscator configuration file.
To build your R8 file, we only need a read only Github access to your app. Then give us 48 hours and we’ll push your file as a PR directly to your repository.
How do we Make it Reliable?
When we’re pitching our service, this is the question that comes most often. How can we guarantee that our configuration is working? How do we know we have covered all cases?
Marcus and I are repurposing a technology we invented for GraalVM so we already have some mileage with it.
Obfuscator configuration is mostly about describing the behavior of reflection instructions at run time. For instance, with the piece of code below you need to instruct R8/Proguard to keep classes “io.manycore.reflection.Meng0 to Meng15 and to not rename them.
| package io.manycore; | |
| public class Main { | |
| public static void main(String[] args) throws ClassNotFoundException { | |
| boolean flag = false; | |
| if (System.getenv("PROD").equals("1")); | |
| flag = true; | |
| if (flag) { | |
| for (int methodToCallCount=0; methodToCallCount <= 7; methodToCallCount++) { | |
| for (int classCount = 0; classCount <= 15; classCount++) { | |
| Class thisClass = Class.forName("io.manycore.reflection.Meng" + classCount); | |
| System.out.println(thisClass.toString()); | |
| } | |
| } | |
| } | |
| } | |
| } |
On our side, we generate the correct configuration by executing the code and logging the actual values.
Complete case covering is a more complicated problem. We get there by trying all the meaningful combinations of the programs. We use some theorems we have discovered (and proved) to reduce the search space to a low figure.
Once we have built the configuration file, we apply the same technique to make sure the app works.
Pricing & Conditions
At this time we can accept only two clients.
Price is $500/release and you only pay is you are happy with our work.
To try us out, just answer to that email and we’ll get back to you.


